mc Trust
mc Trust is the central point of contact to give a transparent overview of measures we take to meet regulatory compliance and protect our systems, secure customer data, and ensure the reliable operation of our services. The information provided showcase the way we adhere to state of the art security standards and regulations and secure our services and products.
You want to report a potential security incident, a vulnerability, or you just have a question about our security? Find the right contact details for our cybersecurity teams here.
Compliance
meteocontrol meets regulatory requirements while continuously improving processes to provide customers with the highest level of assurance regarding data integrity, security, and governance. We follow established standards and proven best practices to ensure a consistent and reliable compliance framework. This is supported by the implementation of effective control mechanisms, including regular audits and structured internal review processes that validate ongoing compliance with all applicable requirements. Beyond that, we have a company-wide culture of responsibility, transparency, and careful handling of sensitive data. With this approach, we ensure that both legal obligations and customer-specific requirements can be reliably met.
ISO 9001
ISO 9001 is an important framework for our company, enabling us to align our processes and procedures with quality and customer satisfaction. The standard helps us consistently deliver high-quality products and services, continuously improve our performance by optimizing our internal processes, and ensure that we meet our customers’ expectations.
ISO/IEC 62443-4-1
Cybersecurity is also a central component of our product development and operational processes. By adhering to the ISO/IEC 62443-4-1 standard, our industrial products are designed, developed, and tested with security in mind at every stage.
ISO 27001
The ISO 27001 standard defines requirements for establishing, implementing, maintaining and continually improving an information security management system. It utilizes a risk driven approach to continuously improve the cybersecurity and business continuity within our organization.
KRITIS audited in accordance with §8a BSIG
By complying with the requirements specified in §8a of the German Act on the Federal Office for Information Security (BSIG) we can assure that our IT systems meet the highest standards of security and reliability and comply with all requirements for critical infrastructure.
Data Center
Physical access control
Physical access to our data centers is restricted to authorized personnel only and secured through multiple layers of protection, including multi-factor authentication.
Data location / residency
All data is exclusively hosted and processed within the European Union, with our infrastructure located in Germany. This ensures that your data remains protected under strict EU and German data protection regulations, including the General Data Protection Regulation (GDPR).
Our data centers are strategically chosen to provide both high availability and strong legal safeguards. By operating entirely within Germany, we benefit from one of the world’s most robust privacy frameworks, giving our customers confidence that their data is handled in accordance with stringent legal and regulatory requirements.
In addition, all hardware used in our infrastructure is fully owned and operated by our company. We do not rely on third-party cloud providers for core data storage or processing. This ownership model allows us to maintain complete control over the physical infrastructure, enforce consistent security standards, and minimize exposure to external risks.
Backups & disaster recovery (DR)
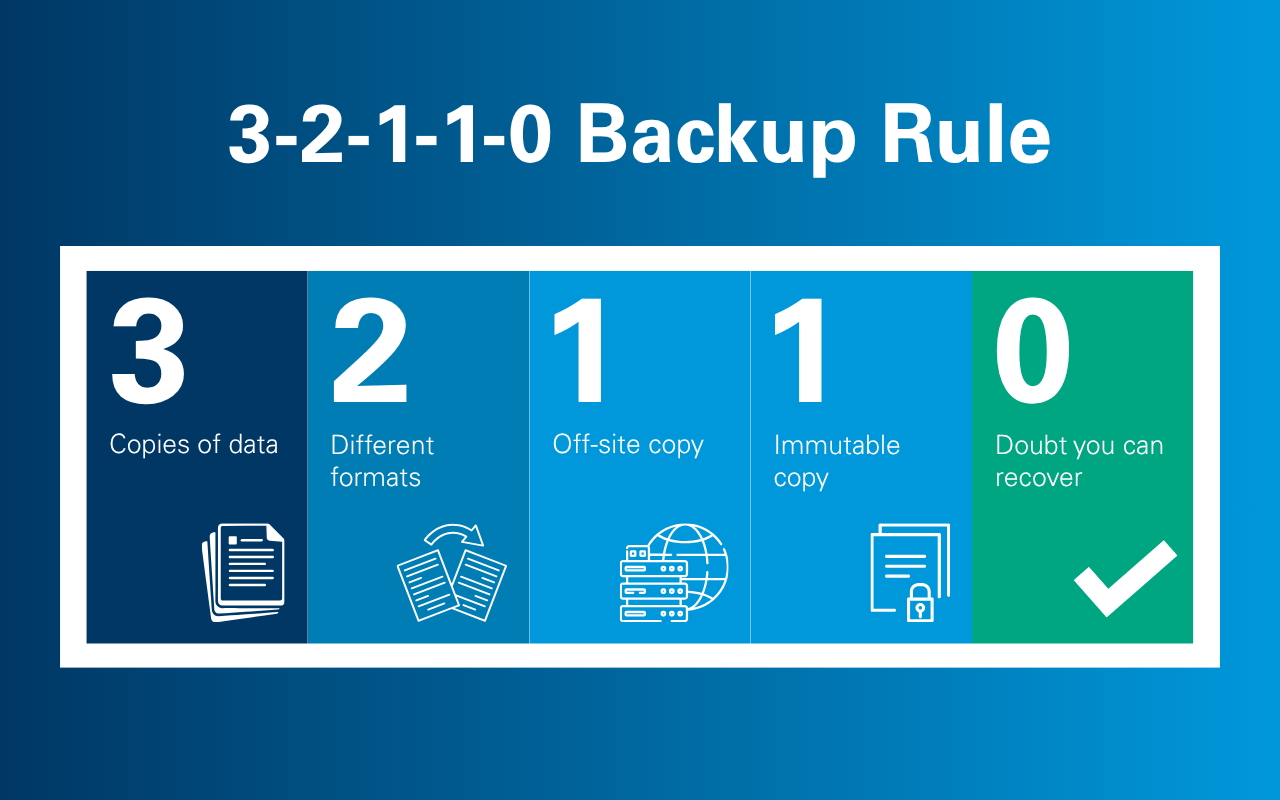
We protect your data using the proven 3-2-1-1-0 backup strategy, ensuring multiple secure copies, including immutable backups, with continuous verification for reliability and integrity.
In the event of a disruption, our recovery process is structured to minimize downtime and restore operations quickly:
- Infrastructure Restoration – We quickly rebuild required systems and environments.
- Secure Backup Import – Your data is restored from a dedicated data center.
This approach ensures fast, reliable recovery while keeping your business operational, even during critical events and advanced cyber threats like ransomware and insider attacks.
Data center reliability & security
Our data center is built to ensure high availability, strong physical security, and reliable operations:
- Certified Standards – ISO 27001 and DIN EN 50600 compliant
- High Availability – Availability Class 3 for resilient, continuous operation
- Physical Security – Protection Class 3 to safeguard against unauthorized access
- Energy Monitoring – Granularity Level 2 for detailed energy tracking and efficiency
- Fire Protection – Gas-based fire suppression system for rapid, damage-free response
- Power Resilience – Uninterruptible power supply (UPS) and emergency generators ensure continuous power
- 24/7 Monitoring – Video surveillance for continuous security oversight
Availability
Our services are built on a redundant and scalable architecture to ensure high reliability. We have maintained an availability of over 99.9% over the past five years, with systems continuously monitored 24/7 to quickly detect and address any disruptions.
Infrastructure security
Our infrastructure is protected through multiple security layers, using controls such as network segmentation, intrusion detection (NIDS), and Distributed-Denial-of-Service-Angriff (DDoS) protection to safeguard systems and availability.
Security at meteocontrol
Security Operation Center (SOC)
We use an external Security Operations Center (SOC) that provides 24/7 monitoring, detection, and response to identify and address security incidents early on. It operates in compliance with BSI-OH-SzA regulations at ML3 and ensures structured processes, continuous log analysis, and an effective response to incidents.
Vulnerability management
Our systems are protected through internal and external vulnerability scans. This allows us to identify potential risks, classify them according to their risk level and remediate them following a defined process.
Logging and monitoring
We use a comprehensive logging system across all our systems to capture and record relevant security and operational events. Our environment is monitored 24/7 to detect potential threats and suspicious activity. Alerts are immediately reviewed and investigated to provide a rapid and effective reaction.
Web Application Firewall (WAF)
Our Web Application Firewall (WAF) helps us to protect meteocontrol`s public accessible web applications from common attacks. The WAF rules are continuously monitored and modified based on operational and security needs.
Security audits
We conduct regular internal audits to review and strengthen our security controls, processes, and compliance with established standards. In addition, independent external audits are performed to obtain an independent assessment of our security and compliance status.
Encryption in transfer
All communication with meteocontrol`s services is encrypted using the industry-standard HTTPS/TLS (TLS 1.2 or higher) over public networks. This ensures that all data traffic with us is secure.
Penetration tests
We hire third parties to perform regular security assessment and penetration testing of our products. Findings are analyzed and addressed through a structured remediation process to continuously enhance our security controls.
Seperation of system environments
To ensure secure development and stable service delivery, we maintain strict segregation of production, development and test environments. This structure minimizes risks and protects production systems from experimental changes.
Product security
Explore the security features of our products, designed with a Secure Development Environment, secure coding standards, and structured vulnerability treatment processes aligned with our Cyber Security Management System (CSMS).
Contact us
Security Incident Response
| Product Security Incident Response Team (PSIRT) | Incident Response Team that manages and resolves security vulnerabilities in our products, ensuring prompt fixes and clear communication to safeguard our customers. | psirt@meteocontrol.com |
| Cybersecurity Incident Response Team (CSIRT) | Incident Response Team that monitors, investigates, and responds to security incidents across our systems and services (including SaaS) to protect data and maintain service availability. | csirt@meteocontrol.com |
Contact us
| General contact for cybersecurity and information security topics | security@meteocontrol.com |